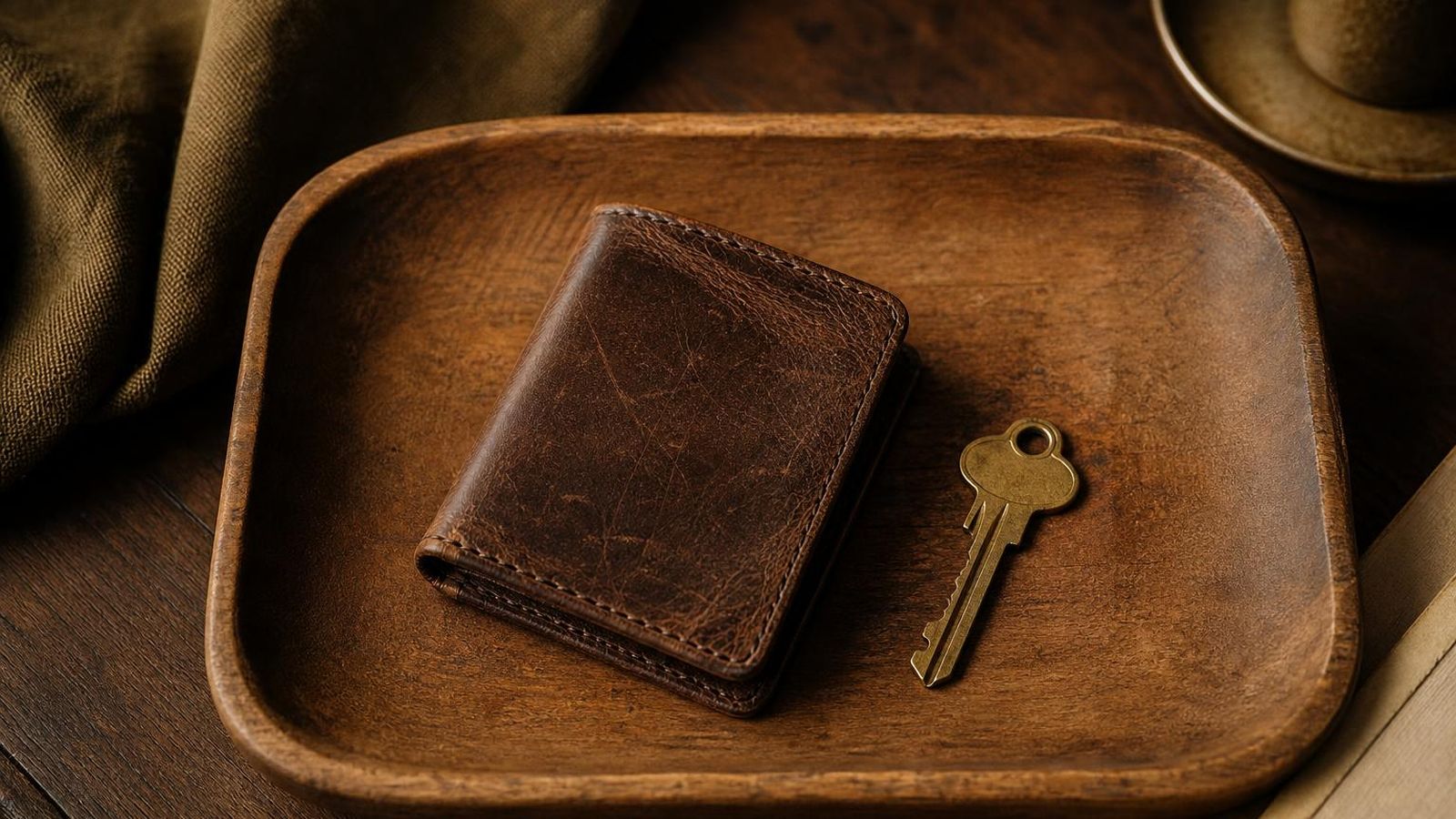
A wallet does not literally hold coins. It holds keys that prove you control addresses on the public ledger. Lose the keys, lose the coins. Share the keys, share the coins. Almost every safety habit on this page comes back to that single sentence.
Custody types
There are two broad categories of wallet, with a third in the middle.
Custodial wallets are accounts on services where the service holds the keys for you. Exchanges and many beginner-friendly apps work this way. Convenient. You can reset a password, recover from a forgotten device, and contact support. You also depend on the service. If it freezes accounts, restricts withdrawals, or fails, your access depends on the service's processes, not on you.
Self-custody wallets put the keys directly in your control. You hold a seed phrase, you back it up, and you are responsible for it. Independence comes with responsibility. There is no reset button. There is no support line for a lost seed.
Hybrid arrangements exist where multiple keys are needed to spend, with some held by the user and some by a service. They can reduce single-point-of-failure risks but add complexity and rely on the service's design. Beginners should not start here.
Seed phrases
A seed phrase is a list of common words, usually twelve or twenty-four, that encodes the master secret for a self-custody wallet. From the seed, all the addresses and private keys for that wallet can be derived. Anyone with the seed has the wallet. There is nothing else to it.
Treat the seed as the wallet itself. Do not type it into a website. Do not photograph it. Do not store it in a password manager that syncs to the cloud. Do not email it to yourself. Do not paste it into a chat with anyone, including someone claiming to be from support. No legitimate service will ever ask for a seed phrase.
Common backup approaches include writing the words on paper kept in a safe place, or stamping them onto a small metal plate that survives heat and water. Two backups in different physical locations are common. Some readers split the words across multiple locations, which adds complexity and can introduce its own failure modes. Keep things as simple as you can while still being durable.
Hardware wallets
A hardware wallet is a small device whose job is to keep the seed and private keys isolated from a general-purpose computer or phone. Transactions are signed inside the device. The signed message comes out. The keys never leave. Even on a compromised computer, an attacker generally cannot extract the keys.
Choosing a hardware wallet is outside the scope of this guide because recommending specific products would create the kind of affiliate dynamic this site does not allow. General principles: buy from the manufacturer or an authorised retailer, check the device on first power-on, set up the seed yourself rather than using anything that came pre-printed, and verify the manufacturer's documentation about firmware and updates.
Address checks
When you send to a new address, check the full address before sending. Malware on a device can replace the address you copied in the moment between copy and paste, leaving the first and last few characters looking similar so a quick glance does not catch the change.
Send a small test transaction first. Wait for it to confirm. Then send the rest. The cost of a test transaction is small. The cost of sending an entire balance to the wrong address is total.
Daily habits
- Do not log in to financial services on a device you would not also do tax returns on.
- Use unique passwords managed in a reputable password manager.
- Use strong second-factor authentication where available, ideally a hardware key or an authenticator app rather than SMS.
- Do not click crypto-related links from social media direct messages, advertisements, or unsolicited email.
- Bookmark the real web addresses of services you use and reach them from the bookmark, not from search.
- Keep wallet software updated. Read the release notes briefly so you know what changed.
- Treat anyone offering "support" through a channel you did not initiate as hostile by default.
Recovery planning
Plan for the case where you cannot use a wallet anymore: lost device, broken device, forgotten passphrase, or, more delicately, a death in the family. A seed phrase that only one person can find is one accident away from being lost. Some readers leave a sealed letter in a place a trusted person can reach if needed. Some use legal documents that point a fiduciary toward a backup location. Whatever you do, pick something survivable rather than something clever.
What not to do
- Do not enter a seed phrase into any website or app that did not generate it.
- Do not screenshot a seed phrase.
- Do not store a seed phrase in cloud notes, chat history, or email drafts.
- Do not import a seed into multiple wallets to "test" things.
- Do not click "wallet drainer" prompts that appear after visiting an unfamiliar site.
- Do not trust pop-up "support agents" who reach out after you complain about a service publicly.